PRESS RELEASE
Hardwear.io announces the 3rd Hardware Security Training & Conference to be held online, 5-10th July 2021 featuring Keynote Speakers from the Korea Advanced Institute of Science and Technology and Dalhousie University of Canada.
|
Organizer |
Hardwear.io |
|
Event Summary |
3rd Edition Hardware Security Training & Conference |
|
Venue |
Online, Zoom & Discord |
|
Training Conference |
July 5th to 8th 2021 July 9th to 10th 2021 |
|
URL: |
https://hardwear.io/usa-2021/ |
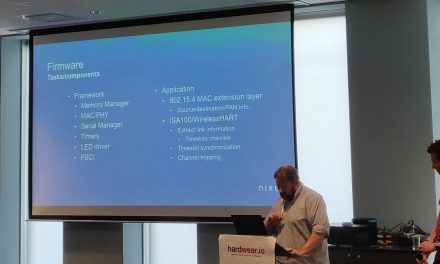
USA – June 23rd 2021: Hardwear.io, USA’s virtual platform for hardware research and innovation, welcomes hundreds of hardware security experts and academia to its 6-day event, July 5-10, 2021. Keynote Speakers will share the latest security research and attack threats to help the hardware and security community to defend their products. More speakers from NCC Group, Google’s OpenTitan project, Riscure and more will share practical insight and tools to the hardware security community.
Many vendors do not always treat hardware security as a priority because of the time and effort involved. That is why platforms and virtual conferences such as Hardwear.io are useful to help InfoSec professionals learn about the latest research and tools they need to protect their IoT devices.
Training sessions:
- Protecting the CAN bus by Ken Tindell, CTO of Canis Automotive Labs
- Assessing and Exploiting PLCs by Justin Searle, Director of ICS Security at InGuardians,
- IC Reverse Engineering & Code Dump by Olivier Thomas, CTO of Texplained
- Reverse Engineering Firmware with Ghidra by Eric Evenchick, Technical Director at NCC Group
- BootPwn: Breaking Secure Boot by Experience by Niek Timmers & Cristofaro Mune, Founders of Raelize
- EMFI and Voltage Fault injection attacks with Raiden by Grzegorz Wypych, Security Researcher at IBM XForce & Adam Laurie, Partner at IBM XForce
- Optimizing Crypto on Embedded Microcontrollers by Peter Schwabe, Research Group Leader at Radboud University & Matthias Kannwischer, PhD Student at Radboud University
If there is a vulnerability on the software side, it can be easily patched, but if there is a vulnerability on the hardware side, it can mean the hardware manufacturer may have to rebuild everything from scratch. The research projects presented at Hardwear.io USA will be used by people who build and secure new silicon products. Members of the audience will become aware of such vulnerabilities, and they will be more sensitive to preventing and fixing them in future products. Moreover, such research also helps companies identify counterfeit products available in the market. This is especially important, as the COVID-19 pandemic has disrupted the balance between supply and demand and counterfeit chips are spreading due to the global semiconductor shortage.
Hardwear.io USA will be held virtually for the second time. Over 1500 hardware security experts from the industry and academia participated in first-ever virtual Hardwear.io USA conference in 2020. The event kicks off with 7 training sessions for 4 days from 5th July 2021, while the Conference will happen between the 9th–10th of July.
Attendees at Hardwear.io will have the opportunity to network and find solutions to address business needs. In addition to the training sessions and conference talks, Hardwear.io has come up with extracurricular activities highly beneficial as they provide its audience useful soft and hard skills through fun and entertaining activities:
Conference is endorsed by Google, NCC Group, NVIDIA, Synacktiv and NXP.














Recent Comments