Details
About the talk
5G mobile networks are around the corner and brags with revised security features from 4G. After a practical investigation we bring to light a new set of vulnerabilities in the 5G/4G protocols and their network operations. Using an inexpensive radio tool set we exploit these vulnerabilities that are found in millions of devices right from the mobile operator’s infrastructure to the end-user devices such as mobile phones, IoT sensors and laptops. Especially, we present automated cellular exploitation tools and also share the traces and data sets with the research community. Our tests are carried out in various continents and highlight vulnerable implementations inside 4G base stations around the world. We target a wide range of devices including the latest NB-IoT chipsets and demonstrate a new class of hijacking, bidding down and battery draining attacks in 4G/5G networks.
Presentation from the talk
Altaf Shaik
Principal Security Researcher at Kaitiaki Labs
Altaf Shaik is a principal security researcher at Kaitiaki Labs and currently pursuing PhD at the Technical University of Berlin. He is experienced in analyzing cellular network technologies from radio to networking protocol layers. His recent renowned research includes low-cost 4G IMSI catchers and security issues in several cellular baseband chipsets.
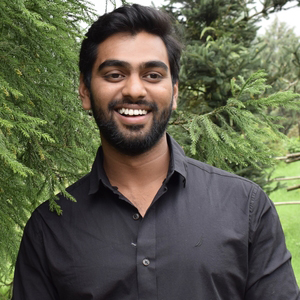
Dr. Ravishankar Borgaonkar
Research Scientist at Sintef Digital
Dr. Ravishankar Borgaonkar works as a research scientist at Sintef Digital and undertakes research in securing next generation digital communication. His primary research themes are related to mobile telecommunication and involved security threats. This ranges from 2G/3G/4G/5G network security to end-user device security. After receiving his PhD in ‘security in telecommunication’ area from the technical university of Berlin, he was a security researcher at Deutsche Telekom’s lab for 3 years. Since that time he has worked for Intel Collaborative Research Institute for Secure Computing at Aalto University, as well as for the University of Oxford focusing on 5G security research. He has found several protocol flaws in 3G/4G technologies and assisted in shaping the 5G security architecture. The demonstrated vulnerabilities affected billions of 3G/4G devices and resulted a change in the existing 3G/4G communication standards.







Recent Comments